What?
I have a couple of machines at home that I would like to be able to access remotely. Now, in the past, the way I’ve done this is:
-
Setup Dynamic DNS on my router - so that home.rraghur.in will resolve to my router.
-
Setup Port forwarding on the router to map an incoming port to port 22 of each internal machine that I want to access remotely.
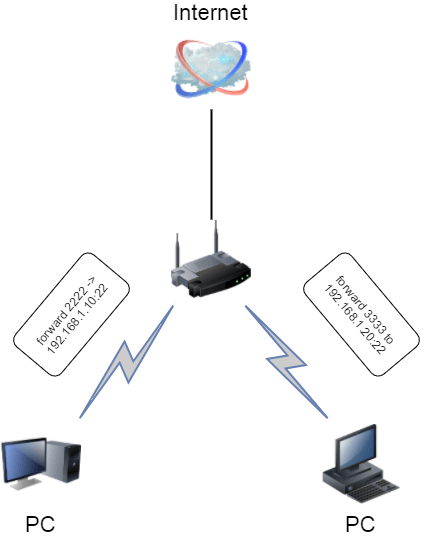 Figure 1. Port forwarding setup
Figure 1. Port forwarding setup -
With the above in place, I could remotely do
ssh -p 2222 home.rraghur.inand ssh into the box.
Now, an year ago when I changed my ISP and a few things changed around my home network, I never bothered to set it up again. Today, I decided to set this up and was in for a few surprises.
Carrier Grade NAT
First things first - I set up my router running Tomato Shibby mod with CloudFlare. DDNS was set up in a jiffy and then I set up the port forwards and tried to SSH in from a remote machine… no luck!
Looking into it, the first clue that something was amiss was that my public IP as seen outside was different from the WAN IP my router was reporting. Turns out that to conserve limited IPv4 space, ISPs themselves use a form of NAT so that multiple customers have a single public IP. With that setup, you can’t actually do port forwarding.
SSH tunnel to the rescue
Turns out that there’s a way around it if you have an external box (VPS or machine in the cloud). What you do is setup each of your internal boxes to have a persistent SSH tunnel to the cloud machine and relay a port from the cloud machine back to your local box.
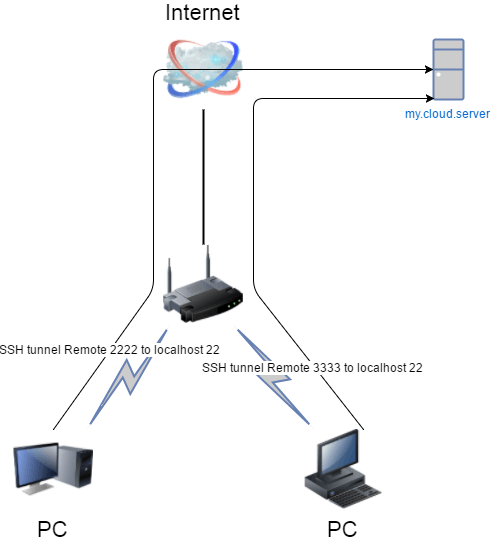
Then when you want to SSH into your machine inside your home network from the
internet, you can do ssh -p 2222 my.cloud.server and voila - you’re in your
home machine.
Here’s a really good post that goes through the details of setting it up.
SSH tunneling is really cool - there’s a ton of fun things you can do with it when the only thing you have is SSH access to a machine. This series of articles walks through more details of SSH port forwarding and something that’s well worth the time.
That’s all for today!